Blockchain & DeFi
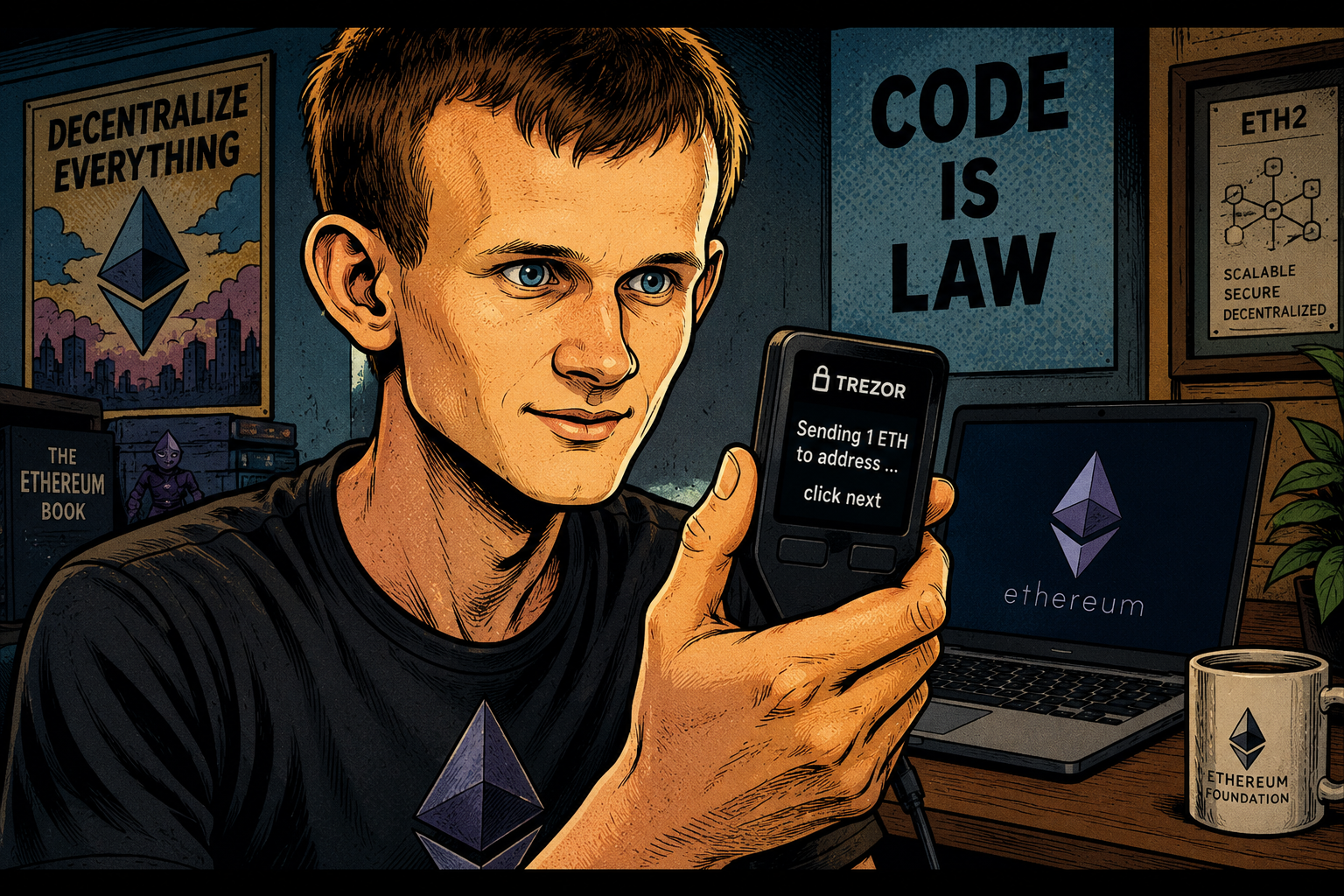
Ethereum Fixes One of Crypto’s Dumbest UX Problems: Users Can Finally Read What They’re Signing
- Share
- Tweet /data/web/virtuals/383272/virtual/www/domains/theunhashed.com/wp-content/plugins/mvp-social-buttons/mvp-social-buttons.php on line 63
https://theunhashed.com/wp-content/uploads/2026/05/vitalik_Trezor-1000x600.png&description=Ethereum Fixes One of Crypto’s Dumbest UX Problems: Users Can Finally Read What They’re Signing', 'pinterestShare', 'width=750,height=350'); return false;" title="Pin This Post">
Crypto has spent years building increasingly sophisticated financial infrastructure while ignoring one embarrassingly basic problem: users often have no idea what they’re approving when they sign transactions. Every day across decentralized finance, NFT platforms, staking protocols, gaming ecosystems, and token launches, users are asked to authorize transactions that appear as unreadable hexadecimal strings, raw contract calls, and opaque permission requests. Most click “approve” anyway because they want the transaction to go through quickly. That behavior has become one of the biggest structural vulnerabilities in the entire digital asset industry.
The Ethereum Foundation is now trying to fix that problem at the infrastructure level. It has launched Clear Signing, a new open standard designed to replace machine-readable transaction prompts with clear human-readable explanations at the exact point where users approve transactions. Instead of signing a transaction that displays a wall of contract data like “0x8f3cf7ad…” users could see straightforward prompts explaining exactly what is happening, such as transferring ETH, swapping tokens, approving NFT access, delegating staking rights, or granting recurring permissions to smart contracts.
It sounds like a minor interface upgrade. It is not. Clear Signing directly targets one of the most common causes of wallet theft, phishing losses, and accidental fund exposure in crypto.
How Blind Signing Became a Multi-Billion Dollar Problem
Blind signing refers to approving blockchain transactions without being able to properly interpret what the transaction actually does. The issue became deeply embedded in crypto infrastructure because smart contracts were originally built for machine execution rather than human readability. Wallets often display transaction payloads exactly as they are transmitted on-chain, leaving users to approve complex interactions without meaningful context.
That design flaw became extremely costly as decentralized finance exploded between 2020 and 2022. Users interacted with yield farming protocols, decentralized exchanges, NFT marketplaces, token bridges, lending applications, and staking products at unprecedented scale. At the same time, phishing attacks became dramatically more sophisticated.
Attackers quickly realized they didn’t always need to hack protocols directly. It was often far easier to trick users into approving malicious transactions themselves.
Fake airdrop websites became one of the most effective scams. Users would connect wallets to claim supposedly free tokens and unknowingly authorize attackers to drain assets. Fraudulent NFT mint pages copied legitimate collections and embedded malicious contract permissions. Fake governance voting portals prompted users to sign harmful approvals disguised as harmless authentication requests.
These attacks repeatedly impacted users of major wallet providers like MetaMask and hardware wallet manufacturers such as Ledger and Trezor.
The problem became especially severe through unlimited token approvals. Many DeFi applications ask users to approve spending permissions for ERC-20 tokens. Rather than approving a single transaction amount, users frequently authorize unlimited access for convenience. If that protocol is later hacked—or if users interact with malicious contracts—attackers can drain token balances without requiring additional approvals.
According to multiple blockchain security firms, phishing and wallet approval scams have consistently ranked among the largest categories of retail crypto losses over the past several years. While bridge hacks and protocol exploits generate bigger headlines, user-side signing errors happen far more frequently.
What Clear Signing Actually Changes
Clear Signing introduces a standardized translation layer between raw blockchain transactions and user-facing wallet interfaces. Instead of showing users raw hexadecimal payloads, participating wallets can interpret transaction intent and present understandable descriptions.
For example, a wallet could now display:
“Swap 5 ETH for 14,500 USDC”
“Grant OpenSea permission to transfer your NFT”
“Approve unlimited USDT access for this smart contract”
“Bridge assets from Ethereum to Arbitrum”
“Delegate 100 ETH to a staking validator”
This sounds obvious, but crypto wallets have historically interpreted transaction data inconsistently. Some wallets show slightly more detail than others. Many show almost none.
Clear Signing creates shared standards so wallet providers, protocols, and developers communicate transaction intent in a more uniform way.
This reduces ambiguity while making suspicious requests easier to detect.
If a malicious website asks users to “grant unlimited access to all NFTs in wallet,” that becomes far harder to ignore than random hexadecimal strings users cannot decode.
Why Industry Cooperation Matters
The most important part of this initiative may be who helped build it.
The Ethereum Foundation is coordinating the standard, but major infrastructure companies contributed to development, including Ledger, Trezor, MetaMask, WalletConnect, and Fireblocks.
That collaboration significantly increases the chances of broad adoption.
Crypto often struggles because every protocol builds isolated systems with little interoperability. Security standards become fragmented and users face inconsistent protections depending on which wallet they use.
An open standard changes that dynamic.
The Ethereum Foundation is intentionally acting as coordinator rather than gatekeeper, allowing developers, wallet providers, decentralized applications, and infrastructure firms to integrate Clear Signing without centralized restrictions.
That approach mirrors successful internet infrastructure standards where widespread adoption matters more than proprietary control.
This Could Reshape Wallet Competition
Wallet providers are increasingly competing on usability rather than simple storage functionality.
For years, wallets primarily differentiated through token support, hardware integrations, and security architecture. But as crypto moves toward mainstream adoption, user experience has become a major battleground.
Clear Signing could become a major competitive feature.
Wallets that deliver better transaction transparency may attract both retail users and institutions seeking stronger operational safeguards.
Institutional platforms like Fireblocks face especially high stakes because transaction errors at enterprise scale can involve millions of dollars.
Retail wallets face a different challenge: reducing friction without overwhelming users with technical warnings.
Clear Signing helps solve both problems.
Why Crypto’s UX Problem Is Bigger Than Most People Realize
Crypto insiders often focus on scaling breakthroughs, ETF flows, institutional adoption, and token launches while ignoring the reality that many products remain intimidating for normal users.
Managing private keys remains stressful.
Gas fees remain confusing.
Wallet recovery systems remain fragile.
Transaction approvals remain opaque.
Even sophisticated users occasionally struggle to interpret complex smart contract interactions involving layer-2 bridges, DeFi vaults, liquid staking protocols, and governance systems.
For mainstream consumers, this friction becomes a major adoption barrier.
Traditional fintech apps rarely ask users to authorize irreversible actions using machine-readable code.
Crypto normalized that absurd experience.
Clear Signing represents a broader philosophical shift where blockchain infrastructure is being forced to become more consumer-friendly.
Will It Actually Stop Crypto Theft?
Not entirely.
Sophisticated phishing attacks will continue evolving. Attackers may create clearer-looking scams, social engineering tactics will remain effective, and some users will continue ignoring warnings.
But Clear Signing dramatically improves baseline security by removing unnecessary confusion.
Scammers thrive when users cannot distinguish normal behavior from malicious behavior.
That advantage weakens when transaction requests become readable.
This won’t eliminate hacks, but it could significantly reduce one of the industry’s most preventable loss categories.
And that makes it one of Ethereum’s most practical upgrades in years.
Not because it increases transaction throughput.
Not because it lowers gas fees.
Not because it introduces flashy new technology.
But because it solves a painful problem that has quietly cost users billions.
Blockchain & DeFi
AI Hackers Are Winning the Crypto Arms Race—And They’re Getting Cheaper Every Two Months

For years, the crypto industry treated artificial intelligence as a growth story. Founders pitched AI trading agents, autonomous DeFi assistants, productivity tools, and automated customer service systems as the next major wave of innovation. But a new report from Binance Research suggests the most disruptive AI trend in crypto may be far darker. According to the firm’s latest data, AI is currently twice as effective at exploiting smart contracts as it is at defending them. The economics are becoming increasingly dangerous. The average cost of launching an AI-powered exploit now sits at roughly $1.22 per contract, making automated attacks extraordinarily cheap to deploy at scale. Even more alarming, Binance Research projects the cost of automated exploitation could fall another 22% every two months, creating a future where scanning thousands of contracts for weaknesses becomes nearly free. That is a nightmare scenario for decentralized finance, where billions of dollars remain locked in immutable code that often cannot be patched quickly once vulnerabilities are discovered.
DeFi Just Suffered Its Worst Month in Over Four Years
The report lands alongside brutal real-world numbers that show the threat is no longer theoretical. DeFi hacks surged to $621 million in April 2026, marking the highest single-month loss total in more than four years. That number alone would have raised alarm bells across the industry, but the deeper breakdown is even more concerning. Roughly 66% of those losses stemmed from compromised access controls, meaning many attacks were not the result of brilliant technical exploits against complex smart contract code. Instead, attackers frequently gained access through admin credentials, governance permissions, compromised private keys, backend infrastructure weaknesses, and operational security failures. This reflects a major shift in attack strategy. Rather than spending weeks finding sophisticated code vulnerabilities, attackers are increasingly targeting easier entry points surrounding protocols. AI makes this strategy dramatically more scalable because phishing campaigns can be personalized instantly, credential attacks can be automated, and vulnerability scanning can happen continuously without human intervention.
Why AI Gives Attackers a Structural Advantage
The economics of cybercrime are changing faster than most crypto teams can adapt. Historically, launching sophisticated attacks required highly specialized technical knowledge, significant manual labor, and large time commitments. AI is rapidly removing all three constraints. Large language models can help malicious actors identify vulnerable code patterns, write exploit scripts, automate phishing campaigns, scan GitHub repositories for exposed credentials, and test attack scenarios faster than traditional human teams. This creates a brutal asymmetry for crypto protocols. Security teams must defend every potential weakness across codebases, wallets, governance systems, internal permissions, employee behavior, and cloud infrastructure. Attackers only need one successful entry point. As offensive AI tools improve faster than defensive systems, smaller protocols may find themselves unable to compete against increasingly industrialized cybercriminal operations.
The Real Problem Is Human Weakness
One of crypto’s original promises was eliminating human trust through smart contracts. In theory, code would reduce reliance on banks, institutions, and human decision-making. In practice, humans remain one of the biggest vulnerabilities in the ecosystem. The latest hack data reinforces that reality. When two-thirds of losses are linked to compromised access controls, the issue often has less to do with broken code and more to do with weak internal processes. Employees click phishing links. Admin wallets get compromised. Teams fail to rotate credentials. Governance systems are poorly structured. Internal operational security remains inconsistent. AI is amplifying all of these weaknesses by making social engineering attacks faster, cheaper, and more convincing. Deepfake calls, AI-generated emails, automated impersonation campaigns, and adaptive scam scripts could become standard attack tools.
Binance Is Fighting Back at Massive Scale
The defensive side is not standing still. Binance says it blocked 22.9 million scam and phishing attempts during Q1 2026, preventing approximately $1.98 billion in user losses. That number reveals both the scale of the threat and the rapid evolution of defensive systems. Crypto exchanges are increasingly investing in AI-powered fraud monitoring, behavioral detection systems, and automated threat identification tools. These systems are becoming essential because manual fraud detection simply cannot keep up with attacks happening at machine speed. The scale of blocked attempts also suggests that users are facing far more attacks than public hack statistics typically reveal.
Tether Has Quietly Become One of Crypto’s Largest Enforcement Players
Tether has become an increasingly aggressive force in crypto crime prevention, even as it remains controversial in broader regulatory debates. The company has frozen more than $4.4 billion in illicit funds to date, demonstrating just how much enforcement power stablecoin issuers now hold within crypto markets. Meanwhile, the T3 Financial Crime Unit—a joint operation involving Tether, TRON, and TRM Labs—froze approximately $300 million in its first year alone. These figures reflect a dramatic shift for an industry that once marketed itself as resistant to centralized intervention. Today, major crypto firms are increasingly acting like quasi-law enforcement partners because the scale of financial crime leaves them little alternative.
Crypto’s Ideological Conflict Is Getting Worse
This defensive evolution creates a growing philosophical problem for crypto. Users want stronger fraud prevention systems, better recovery mechanisms, and faster intervention when funds are stolen. At the same time, many crypto purists remain deeply uncomfortable with centralized entities having the ability to freeze assets, monitor transactions, and cooperate closely with regulators. Tether freezing billions may protect victims, but it also highlights how centralized power continues expanding within supposedly decentralized systems. As AI-driven attacks become more sophisticated, the pressure to centralize defensive infrastructure may intensify even further.
The Future of Crypto Crime Is Autonomous
The most important takeaway from Binance Research is that crypto security is entering a new era defined by autonomous conflict. This is no longer a battle between individual hackers and protocol developers. It is becoming a war between machine-driven offensive systems and machine-driven defense systems. Attackers are scaling faster, costs are collapsing, and exploit automation is improving at alarming speed. If the economics continue moving in this direction, crypto may soon face an environment where attacks become constant, automated, and unavoidable background noise. That would fundamentally reshape how protocols are built, how users interact with DeFi, and how regulators approach the entire sector.
Blockchain & DeFi
Crypto Hacker Returns 90% of Stolen Funds After Project Offers Onchain Deal
Crypto hacks usually end in one of two ways: the attacker disappears forever, or law enforcement spends years chasing wallets across chains with little to show for it. This week, a far stranger outcome played out in DeFi. A hacker who exploited Arbitrum dark pool protocol Renegade and drained roughly $209,000 worth of assets unexpectedly returned about 90% of the stolen funds after the protocol publicly negotiated with the attacker onchain. The exploit initially impacted 27 ERC-20 tokens and looked like another routine DeFi loss. Instead, it turned into one of crypto’s increasingly common “whitehat negotiations,” where protocols effectively settle with attackers in real time to recover user funds before reputational damage spirals.
The Exploit Drained $209K Across 27 Tokens
The original attack targeted Renegade’s dark pool infrastructure on Arbitrum, draining approximately $209,000 across a wide basket of tokens. While the total loss was relatively small compared with billion-dollar protocol exploits that have defined previous cycles, the incident still highlighted a growing problem in DeFi infrastructure: smaller protocols often have fewer security resources while still managing increasingly complex smart contract architectures. Even relatively contained attacks can severely damage user trust, particularly for newer protocols trying to establish credibility in increasingly competitive decentralized finance markets.
Renegade Took an Unusual Approach
Rather than immediately escalating threats or waiting for blockchain investigators to track the attacker, Renegade made a highly pragmatic decision. The team sent an onchain message directly to the exploiter with a simple proposal: return 90% of the stolen funds, keep 10% as a whitehat bounty, and avoid legal consequences. The offer essentially reframed the exploit as a security disclosure rather than outright theft. This strategy has become increasingly common in DeFi because recovering most funds quickly is often more valuable than pursuing lengthy legal battles that rarely result in full restitution.
The message was blunt but effective. Return the funds, keep a six-figure reward, and walk away.
The Hacker Returned $190K
Shortly after receiving the message, the attacker returned roughly $190,000 worth of assets to Renegade. According to the protocol, the hacker claimed the exploit was conducted to protect DeFi users and expose vulnerabilities before more malicious actors could exploit them. Whether that explanation reflects genuine whitehat intentions or simply a calculated effort to avoid legal risk remains unclear.
That ambiguity has become a recurring theme in crypto security incidents. Some attackers initially exploit vulnerabilities before negotiating returns once public scrutiny intensifies. Others may genuinely identify weaknesses but use aggressive extraction tactics to force protocol teams into paying substantial bounties.
In this case, Renegade recovered the overwhelming majority of user funds—which is ultimately what matters most to affected users.
The Rise of “Negotiated Hacking”
This type of event is becoming increasingly normalized across crypto markets. Protocols now frequently negotiate directly with attackers through blockchain messages, social media, and public statements. In many cases, projects offer exploiters a percentage of stolen funds in exchange for returning the remainder. This creates a strange gray zone between ethical hacking, extortion, and practical damage control.
The model exists because traditional legal enforcement remains difficult in decentralized systems. Attackers often operate anonymously, move funds across chains, and exploit jurisdictional gaps that make prosecution difficult. Negotiation becomes the fastest path toward recovering user capital.
It may feel unconventional, but the strategy often works better than courtroom battles.
DeFi Security Still Has a Massive Problem
Even though this story ended relatively well, it reinforces a larger issue across decentralized finance. Smart contract vulnerabilities remain one of the sector’s biggest structural weaknesses. As protocols introduce more advanced trading systems, dark pools, cross-chain bridges, synthetic assets, and AI-powered trading infrastructure, the attack surface continues expanding.
Security audits help but are not foolproof. Bug bounty systems help but remain underutilized. Formal verification remains expensive. Meanwhile, attackers continue becoming more sophisticated.
The industry still loses billions annually to exploits, hacks, and protocol failures.
Why This Story Matters
The biggest takeaway is not that Renegade got lucky—it’s that crypto’s security culture is evolving. Protocol teams are becoming more pragmatic, attackers increasingly understand public pressure, and users are starting to see more funds recovered after incidents that once would have been permanent losses.
That does not solve DeFi’s security challenges, but it does show the industry is developing faster mechanisms for crisis response.
This time, a hack ended with users getting most of their money back.
In crypto, that still counts as an unusually good outcome.
Blockchain & DeFi
$17 Billion Stolen: A Decade of Crypto Hacks Exposes the Industry’s Deepest Flaw

For an industry built on the promise of trustless systems and cryptographic certainty, the numbers tell a different story. Over the past decade, crypto hackers have siphoned off more than $17 billion across 518 separate incidents, according to DeFiLlama. That breaks down to an average of roughly $33 million per exploit—and perhaps more alarmingly, a major breach nearly every single week for ten years straight.
This is no longer a series of isolated failures. It’s a systemic pattern, one that continues to test the very foundations of decentralized finance.
The Anatomy of a $17 Billion Problem
The scale of crypto-related theft has evolved alongside the industry itself. Early exploits often targeted basic smart contract vulnerabilities or poorly secured exchanges. Today’s attacks are more sophisticated, more targeted, and far more lucrative.
What stands out in the latest data is not just the total value lost, but how those losses are occurring. The largest share—over $3.6 billion—has been attributed to private key compromises. These are not bugs in code or unforeseen protocol flaws. They are direct breaches of the most fundamental layer of crypto security: ownership.
Private keys are supposed to be unbreakable under proper cryptographic assumptions. But in practice, attackers have exploited weak key generation, phishing attacks, social engineering, and brute-force techniques to gain access. Once a private key is compromised, there is no recourse. Funds can be moved instantly, irreversibly, and often anonymously.
The implication is stark. The weakest point in crypto is no longer the protocol—it’s the interface between humans and security.
2025: The Breaking Point
If the past decade tells a story of gradual escalation, 2025 marks a clear inflection point. Losses surged past $4.04 billion, making it the worst year on record for crypto-related hacks.
This spike was not driven by a single catastrophic event, but rather a cluster of large-scale exploits across decentralized finance platforms, bridges, and infrastructure layers. The increasing complexity of DeFi systems—stacked protocols, cross-chain interactions, and composability—has created an expanded attack surface that adversaries are learning to navigate with precision.
In many cases, attackers are no longer lone actors. Organized groups, some suspected to be state-backed, are now operating with the sophistication of professional cyber operations. They conduct reconnaissance, exploit vulnerabilities, and launder funds through intricate on-chain and off-chain pathways.
The result is an environment where high-value targets are continuously probed, and eventually, breached.
The Rise of Bridge Attacks
Among the most vulnerable components in the crypto ecosystem are cross-chain bridges. These systems are designed to move assets between blockchains, but in doing so, they often rely on complex validation mechanisms and pooled liquidity—both of which present attractive targets.
The recent exploit involving Kelp DAO underscores this risk. Its rsETH bridge was drained of approximately $290 million, marking the largest DeFi hack of 2026 so far.
Bridge attacks are particularly damaging because they concentrate large amounts of capital in a single point of failure. When compromised, the losses are immediate and massive. Moreover, the interconnected nature of DeFi means that the impact can cascade across multiple protocols, amplifying systemic risk.
A Weekly Crisis Becomes Normalized
Perhaps the most troubling aspect of the data is how routine these incidents have become. One major exploit per week is no longer shocking—it’s expected.
This normalization has profound implications for investor behavior and institutional adoption. While seasoned crypto participants may factor in security risks as part of the landscape, traditional financial institutions operate under very different assumptions. Persistent, high-value breaches create a perception of instability that is difficult to reconcile with fiduciary standards.
Yet, paradoxically, the market continues to grow. Capital flows into DeFi, new protocols launch, and innovation accelerates. This suggests that the industry has, to some extent, priced in the risk of hacks as a cost of doing business.
That may be sustainable in the short term. In the long term, it raises deeper questions about resilience.
Security Theater vs. Structural Change
In response to the surge in exploits, many projects have doubled down on security measures: audits, bug bounties, and formal verification processes. While these are necessary steps, they are not sufficient.
Audits, for example, are snapshots in time. They cannot account for evolving attack vectors or unforeseen interactions between protocols. Bug bounties incentivize disclosure, but only within certain boundaries. And formal verification, while powerful, is limited by the assumptions it is built upon.
What is increasingly clear is that incremental improvements are not enough. The industry may need to rethink its approach to security at a structural level.
This could include more widespread adoption of multi-signature wallets, hardware-based key management, and decentralized validation systems that reduce single points of failure. It may also involve reimagining user experience to minimize the likelihood of human error—a factor that continues to play a central role in many exploits.
Regulation Enters the Conversation
As losses mount, regulatory pressure is intensifying. Policymakers are beginning to view security failures not just as technical issues, but as consumer protection concerns.
In the United States, ongoing debates around market structure legislation—such as the proposed CLARITY Act—are increasingly intersecting with questions of security standards and accountability. If billions of dollars can be lost through preventable vulnerabilities, regulators are likely to demand stricter safeguards.
This introduces a new dynamic. Greater oversight could enhance security and restore confidence, but it may also constrain the permissionless innovation that defines DeFi.
Striking the right balance will be one of the defining challenges of the next phase of crypto’s evolution.
The Road Ahead
The $17 billion figure is more than just a statistic. It is a reflection of an industry still in the process of maturing, grappling with the tension between openness and security.
For builders, the message is clear: security can no longer be treated as a secondary consideration. It must be embedded into every layer of design, from protocol architecture to user interaction.
For investors, the landscape demands a more nuanced approach to risk. Yield opportunities must be weighed against the structural vulnerabilities that continue to surface.
And for the industry as a whole, the path forward will likely involve a combination of technological innovation, cultural shifts, and regulatory evolution.
Crypto was designed to eliminate the need for trust. Ironically, its future may depend on rebuilding it—this time, on stronger foundations.
-

 Cardano8 months ago
Cardano8 months agoCardano Breaks Ground in India: Trivolve Tech Launches Blockchain Forensic System on Mainnet
-

 Cardano6 months ago
Cardano6 months agoSolana co‑founder publicly backs Cardano — signaling rare cross‑chain respect after 2025 chain‑split recovery
-
 Cardano8 months ago
Cardano8 months agoCardano Reboots: What the Foundation’s New Roadmap Means for the Blockchain Race
-

 Altcoins5 months ago
Altcoins5 months agoCrypto Goes Mainstream — Bitwise 10 Crypto Index ETF (BITW) Debuts on NYSE Arca
-

 News5 months ago
News5 months agoCrypto on Trial: The $5.5 Billion Pump.fun, Solana & RICO Lawsuit That Could Redefine On‑Chain Liability
-

 News5 months ago
News5 months agoFrom Memes to Courtrooms: Solana and Jito Execs Named in Explosive RICO Suit Over Pump.fun
-
 Altcoins6 months ago
Altcoins6 months agoNYSE Arca Files to Launch Altcoin-Focused ETF
-

 News4 months ago
News4 months agoSenate Postpones CLARITY Act Vote Amid Crypto Industry Revolt: Inside the Growing Divide